Introduction:
Introduction:
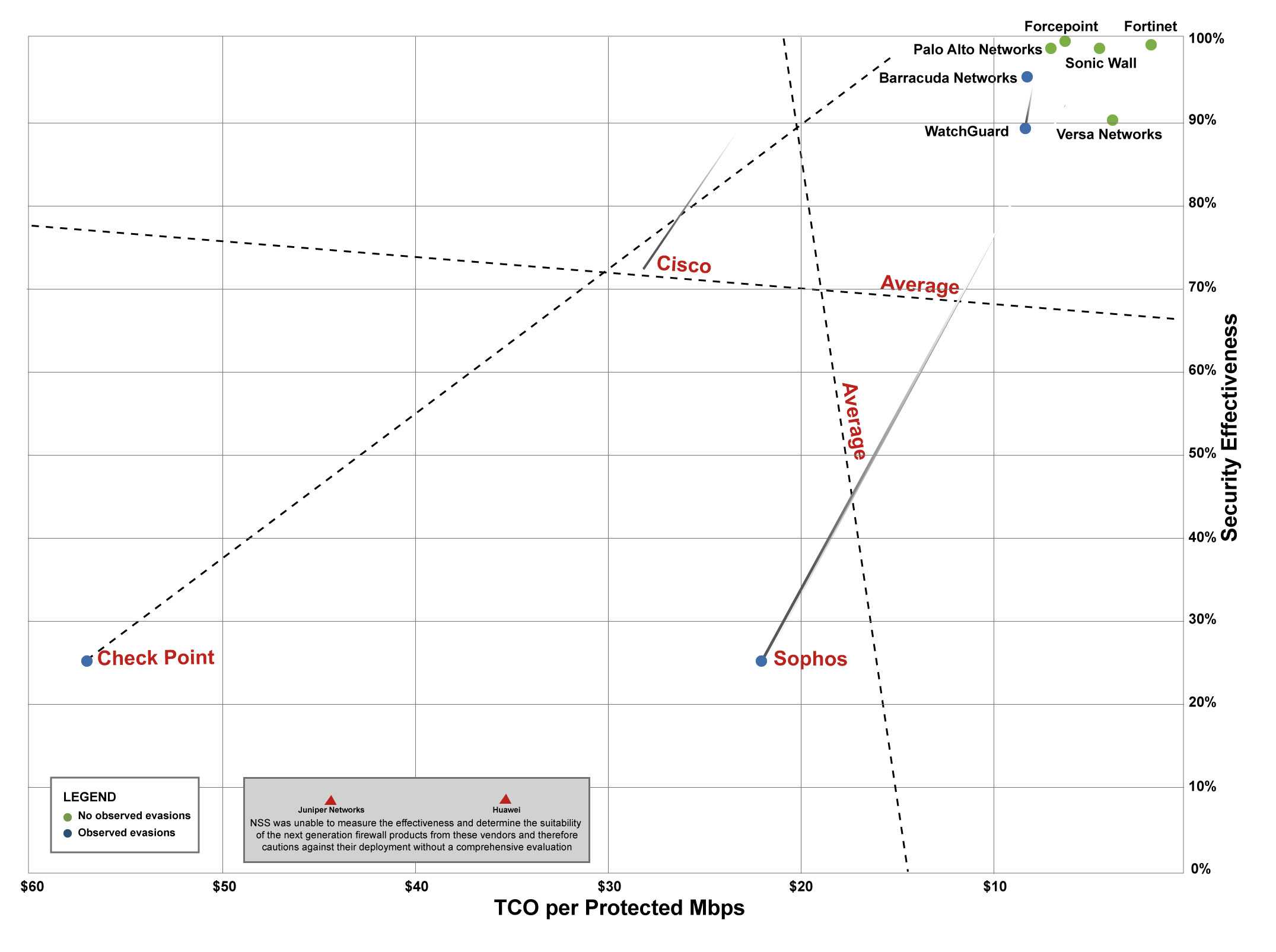
An evasion is a procedure which targets security systems with the primary objective of avoiding detection. Once the evasion has succeeded, an attacker may be empowered to deliver a malicious payload to the systems behind the security barrier. Many evasion methods exist for firewalls, intrusion detection devices, deep inspection routers and other network security devices.

 The sheer volume of possible evasion combinations has challenged many cyber security vendors and resulted in several firewalls and IPSs currently installed being blind to sophisticated attacks based on AETs. Based on our extensive research we believe that the Forcepoint next generation firewall (NGFW) provides the best protection against exploits that leverage AETs. A pioneer in research on AETs, Stonesoft exposed the technique to the world in 2010 and developed the firewall to detect and protect networks against malicious code delivery through AETs. The Forcepoint NGFW has been successfully tested against more than 800 million AET variants.
The sheer volume of possible evasion combinations has challenged many cyber security vendors and resulted in several firewalls and IPSs currently installed being blind to sophisticated attacks based on AETs. Based on our extensive research we believe that the Forcepoint next generation firewall (NGFW) provides the best protection against exploits that leverage AETs. A pioneer in research on AETs, Stonesoft exposed the technique to the world in 2010 and developed the firewall to detect and protect networks against malicious code delivery through AETs. The Forcepoint NGFW has been successfully tested against more than 800 million AET variants.